Continuous Network Security Policy Management from
Visibility to Automated Action
Opinnate helps security teams analyze policies, reduce risk, and apply controlled changes across hybrid environments.











“Proven in complex, regulated environments where audit readiness and change safety matter.”

90%
Discover why leading enterprises trust Opinnate to deliver governed network security results.
Continuous Risk Analysis
Reduce policy risk with real-time analysis and prioritization of vulnerabilities across your entire network estate.
Optimization Workflows
Cut manual effort by up to 90% with automated optimization and clean-up workflows.
Audit-Ready Reporting
Accelerate compliance with scheduled, export-ready reports for PCI-DSS, HIPAA, and more.
Network Visibility
Gain complete visibility into internal applications and user access patterns.
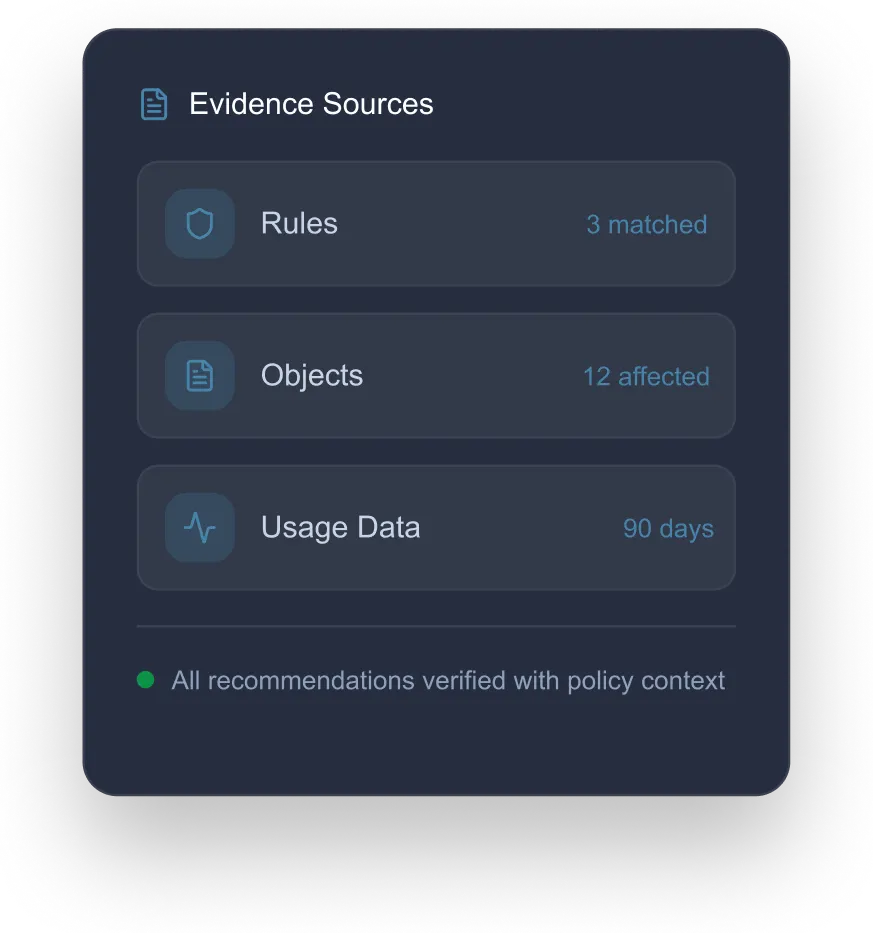
Shadowing, usage insights, topology, and historical context


Opinnate helps security teams analyze policies, reduce risk, and apply controlled changes across hybrid environments.
- "Why is this application blocked?"
- "Show unused rules in the last 90 days..."
- "Remove the old DMZ database server..."
Explore our comprehensive security services designed to automate, optimize, and drive resilience tailored to your network.
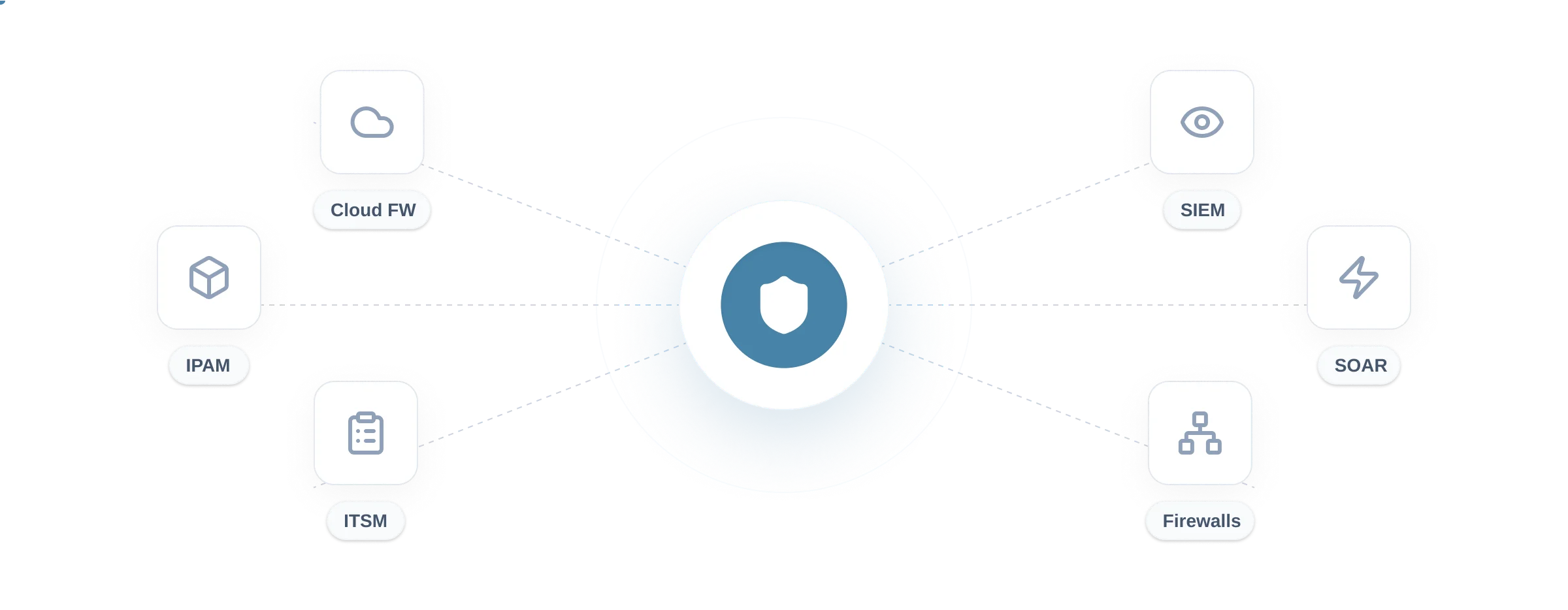
Implement granular access controls to minimize attack surface and prevent lateral movement.
Unified policy management across AWS, Azure, and Google Cloud Platform environments.
Connect to on-prem and cloud firewalls, SIEM/SOAR/ITSM, and IPAM to turn insights into governed change.








Scale your security governance from insights to full automation.
Analysis & reporting for small teams getting started with visibility.
- Shadow rule analysis
- Basic topology mapping
- 90-day history
- PDF Reports
- Email support
- Policy visibility & insights
- Usage analysis (incl. passive monitoring)
- Custom reports & scheduling
- Best for: Teams starting with visibility, hygiene, and audit readiness
Optimization actions for growing organizations needing hygiene.
- Everything in Lite
- Guided cleanup actions (unused/expired, dedupe objects, consolidation)
- Scheduled optimization tasks
- Best for: Teams ready to safely reduce policy waste
- Everything in Lite
- Automated rule cleanup
- Object optimization
- Scheduled maintenance
- API Access
- Priority support
Full automation & lifecycle governance for large scale operations.
- Everything in Standard
- Zero-touch automation
- Policy change workflows
- Custom compliance reports
- Multi-tenant support
- Dedicated success manager
- Everything in Standard
- Governed rule/object automation workflows
- Lifecycle management (expiring rules, periodic reviews)
- Best for: Teams scaling change volume with control and traceability
App Mapping & Monitoring
License Tracking
Certificate Tracking
Firewall Backup
Switch Hardening
Get a tailored walkthrough based on your firewall vendors, policy complexity, and audit needs.
Get a personalized walkthrough
By submitting, you agree to our Privacy Policy

Head Quarters:
8, 320 Tubbenden Lane South, Bromley, BR6 7DN, United Kingdom

R&D:
Kazlıçeşme Mah. 245. SK. 5 Zeytinburnu/İstanbul Türkiye
Request your demo or get detailed information by completing this form.
- G2 High Performer
- SOC2 Type II Compliant


