Network Microsegmentation and Zero Trust
The Problem
Network Microsegmentation ensures that, as the zero-trust security model requires, only intended users and devices can access applications and servers they have been designated to, by taking network and security policies down to workload level. This is crucial considering that networks no longer have perimeters, the cyber attack surface has expanded, and cyber criminals have the techniques to move across different network segments once defenses are evaded.
While crucial, implementing and managing micro-segmentation can be complicated. It requires knowledge of the applications involved, well-defined policies, and a system in place to keep up with ongoing changes that need to be made across a multitude of policies.
Automation of Microsegmentation Policy Management
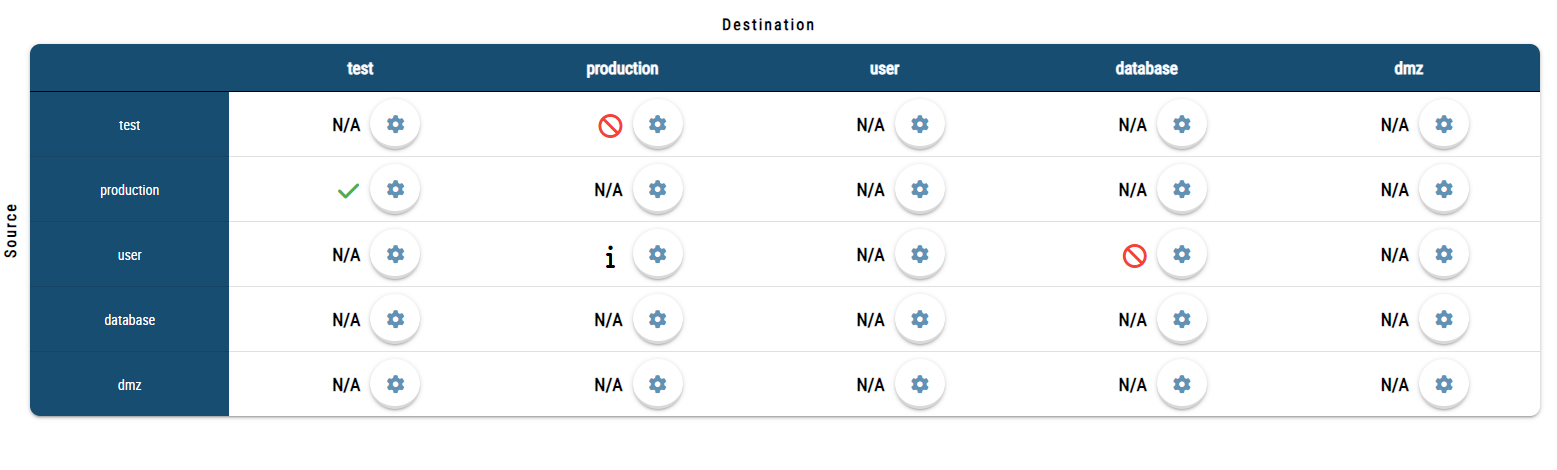
Policy automation and rule optimization are essential components of successful network microsegmentation projects, whether implemented in on-premise networks, data centers, or cloud environments. IT teams need to be enabled by an intelligent and lightweight automation technology so that microsegmentation projects do not become cumbersome, but rather work seamlessly to segment applications, servers, and networks into the smallest units possible to ensure security and compliance.


Opinnate Enables Successful Microsegmentation & Zero Trust Networks
By extending network security policy management to microsegmention, the Opinnate platform help IT teams to;
- Easily apply least privilege principle in policy setting.
- Set well-defined, granular and easy to manage policies.
- Avoid errors.
- Automate policy approval and rejection based on corporate policy.
- Continuously monitor and analyse policies across complex and hybrid environments.
Why Opinnate?
What are the differences?
- All-in-one policy management
- No need for a management product from any firewall vendor
- More use case scenarios for real needs
- Short deployment and enablement
Why are these good for you?
- Lower TCO
- A comprehensive but simpler-to-use solution
- Less dependency to tools (Firewall management consoles, firewall analyzer)
- Less resource usage


