How Network Policy Change Automation Helps Maintain Compliance in Dynamic Environments

Blog Overview Modern businesses operate in fast-changing digital environments where security rules must evolve constantly. Manual updates often create delays, errors, and compliance risks. In this blog, you will discover how network policy change automation helps businesses maintain compliance, improve visibility, and reduce operational stress. You will also learn practical examples, benefits, and how to choose the right solution for your business. Understanding Compliance Challenges in Modern Networks Businesses today rely on cloud platforms, remote access, and digital transactions. As networks expand, maintaining compliance becomes more complex. Manual firewall updates often lead to inconsistent policies, missed approvals, and security gaps. For shop owners and growing businesses, this means increased risk and wasted time. A simple rule change for a payment system or inventory platform may require multiple approvals and documentation. Without network policy change automation, tracking these changes becomes difficult and error-prone. This is where automation plays a critical role. It helps maintain consistency while ensuring compliance with industry standards and internal policies. The Growing Need for Network Policy Change Automation Network policy change automation simplifies how businesses manage security rules. It automatically validates policy changes, tracks approvals, and ensures compliance requirements are met. With firewall policy automation for enterprises, organisations gain visibility across their entire network. This means teams can identify potential risks before they impact operations. For example, a retail business launching a new online store may need new firewall rules. Instead of manually configuring settings, automation tools review the request, check compliance, and apply changes safely. Firewall change management automation also provides audit trails. This makes it easier to demonstrate compliance during audits or security reviews. Everyday Business Scenarios Where Automation Helps Many businesses experience frequent network updates. For instance, a shop owner adding a new payment gateway needs secure access policies. Automation ensures the new rule follows compliance requirements without manual errors. Another example is seasonal sales events. Increased traffic often requires temporary policy changes. Network security policy management tools help businesses safely implement these updates while maintaining compliance. These practical scenarios show how automation supports daily operations while reducing risk. Compliance Benefits That Go Beyond Security Automation delivers benefits beyond compliance. It improves efficiency, reduces downtime, and enhances collaboration between teams. When using network policy change automation, businesses save time on manual approvals and documentation. Teams can focus on growth instead of routine tasks. In many cases, automation also reduces human error. This improves overall security posture and prevents costly disruptions. Additionally, firewall policy automation for enterprises provides better visibility. Businesses gain insights into policy performance and potential risks. Why Automation Supports Business Growth and Confidence Security is not only about protection. It is also about confidence. When businesses rely on automated policy management, decision-makers feel more comfortable implementing changes. For example, a growing e-commerce store expanding to new regions may require new access controls. With firewall change management automation, these updates happen smoothly and securely. This confidence allows businesses to innovate faster without compromising compliance. Choosing the Right Automation Strategy Choosing the right solution depends on business needs. Start by identifying how often your network changes. Frequent updates often require advanced automation features. Look for tools that support network security policy management with clear reporting and approval workflows. This ensures compliance and operational transparency. Businesses should also prioritise solutions that integrate with existing infrastructure. This reduces complexity and speeds up implementation. Final Thoughts Dynamic environments demand flexible and reliable security management. Network policy change automation helps businesses maintain compliance, reduce risk, and improve operational efficiency. From shop owners to growing enterprises, automation simplifies complex security tasks while supporting business growth. If you are looking to strengthen compliance and streamline security operations, explore solutions from Opinnate and discover how automation can transform your network management strategy. Frequently Asked Questions 1. What is network policy change automation? Network policy change automation is a process that automatically manages firewall and network rule changes while ensuring compliance and security standards. 2. How does firewall policy automation for enterprises improve compliance? It validates changes, tracks approvals, and maintains audit logs, which helps organisations meet compliance requirements. 3. Is firewall change management automation suitable for small businesses? Yes. Even small businesses benefit from reduced manual effort and improved security visibility. 4. How does network security policy management help businesses? It centralises policy control, reduces errors, and ensures consistent compliance across networks. 5. When should a business adopt network policy change automation? Businesses should adopt automation when network changes become frequent, complex, or difficult to track.
How to Enable Network Policy Change Automation across Multi Vendor Firewall Environments
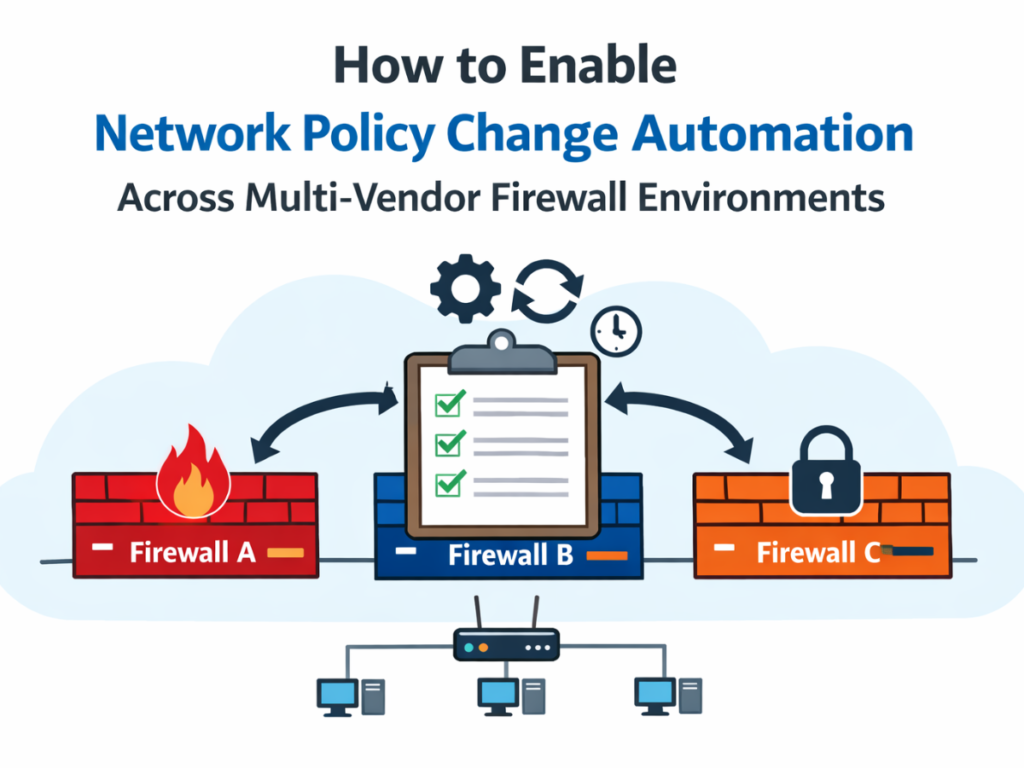
Blog Overview This blog explores how organizations can automate firewall changes across different vendors while improving operational efficiency. You will learn why automation matters, when to implement it, how to choose the right approach, and the long term benefits of automated security policy management. Introduction Managing security across multiple firewalls from different vendors can quickly become complex. Many businesses struggle with inconsistent rules, delayed approvals, and increased security risks. In this blog, you will learn how to implement network policy change automation across multi vendor firewall environments. You will also discover practical strategies, real world scenarios, and how automation improves visibility and compliance. For businesses that rely on secure and scalable infrastructure, automation is no longer optional. With growing cloud adoption and hybrid networks, firewall change management automation helps teams reduce manual work while improving security posture. The Challenge of Multi Vendor Firewall Environments Many organizations use firewalls from different vendors to meet various operational needs. While this provides flexibility, it also creates complexity. Security teams often manage different interfaces, rule formats, and approval workflows. For example, a security engineer might need to update rules on multiple firewalls manually. This process increases the chance of errors and delays. Without network security policy management, teams struggle to maintain consistency across environments.Manual processes also slow down business operations. When application teams request access changes, delays can impact productivity and customer experience. Importance of Network Policy Change Automation Implementing network policy change automation helps organizations standardize processes across vendors. Automation tools provide centralized visibility, automated approvals, and compliance checks. This means security teams can Reduce manual errors Speed up change approvals Maintain compliance with policies Improve visibility across environments In many cases, automation also helps organizations respond faster to security threats. Instead of manual updates, automated workflows apply changes quickly and accurately. Real- Life Cases Where Automation is Useful Businesses often face situations where firewall changes are frequent. For example, a retail company launching a new online store needs to update multiple firewalls. Without firewall change management automation, this process could take days. Another scenario involves cloud migration. As companies move applications to cloud environments, firewall policies need constant updates. Automated security policy management ensures changes are consistent and compliant. These real world examples show how automation improves both agility and security. Benefits of Network Security Policy Management beyond Cost Savings Automation delivers more than financial savings. It improves operational efficiency and reduces risks. Key benefits include Faster deployment of applications Improved compliance and audit readiness Reduced human errors Better collaboration between teams Increased network visibility With network security policy management, organizations gain control over their security environment while supporting business growth. Picking the Right Automation Strategy Selecting the right approach requires careful planning. Businesses should consider the following factors Compatibility with multiple firewall vendors Integration with existing security tools Policy standardization capabilities Automation workflow flexibility Reporting and compliance features Many organizations also benefit from starting with a phased approach. Begin with high impact policies, and then expand automation gradually. A Smarter Way to Manage Security Policies Modern businesses need flexible and scalable security solutions. Network policy change automation allows teams to adapt quickly while maintaining strong security standards. For example, organizations using hybrid infrastructure often rely on automation to maintain consistent rules across data centers and cloud environments. This approach simplifies operations and strengthens security posture. Final Thoughts Managing multi vendor firewalls does not have to be complicated. With firewall change management automation and automated security policy management, organizations can streamline operations, improve compliance, and reduce risks. If your business is looking to simplify firewall operations and improve security efficiency, explore automation solutions from Opinnate. Visit our website to learn how intelligent network security policy management can transform your infrastructure and help your team work smarter. Frequently Asked Questions 1. What is network policy change automation? Network policy change automation is the process of automating firewall rule updates and policy changes across multiple systems to improve efficiency and reduce errors. 2. Why is firewall change management automation important? It reduces manual work, improves compliance, and speeds up security updates across multiple firewall vendors. 3. Can automation work across different firewall vendors? Yes, modern automation platforms support multi vendor environments and provide centralized control. 4. How does automated security policy management improve compliance? Automation ensures policies follow predefined rules and maintains audit ready documentation. 5. When should businesses implement network security policy management? Businesses should implement it when firewall complexity increases, changes become frequent, or compliance requirements grow.
How Network Policy Change Automation Is Transforming Security Operations in 2026

Blog Overview This blog explores how automation is reshaping security operations in 2026. You will learn why businesses are adopting automation, when it becomes necessary, and how it improves firewall rule change management. We will also share practical examples and tips to help you make informed decisions. Introduction Security operations are evolving faster than ever. Businesses today manage complex infrastructures, cloud platforms, and multiple firewalls while trying to maintain strong protection. Manual processes often slow teams down and create unnecessary risks. In this blog, you will learn how network policy change automation is transforming security operations in 2026. You will also discover how automation improves efficiency, reduces errors, and helps businesses scale securely. For modern organisations, especially shop owners managing online platforms, secure networks are essential. With growing digital transactions and customer data handling, network security policy management is becoming a critical part of business success. The Growing Challenge in Security Operations Security environments have become more complex than ever before. Businesses often use multiple firewalls, cloud platforms, and applications. Managing these manually increases workload and creates inconsistencies. For example, a shop owner launching a new e-commerce platform may need to update firewall rules quickly. Without firewall rule change management, delays can affect website performance and customer experience. In many cases, manual updates also increase the risk of configuration errors. This is why businesses are turning to network policy change automation to simplify operations and improve security. Why Network Policy Change Automation Matters in 2026 In 2026, automation is no longer a luxury. It is a necessity. Network policy change automation helps organisations streamline workflows and ensure consistent security policies. Automation helps businesses Reduce manual errors Speed up policy approvals Improve compliance tracking Increase visibility across systems Enhance collaboration between teams With network security management, organisations can respond quickly to changing security requirements while maintaining operational efficiency. Real-World Scenarios Where Automation Makes a Difference Consider a retail business preparing for seasonal sales. Traffic increases significantly, and new applications must be deployed quickly. Manual firewall changes can delay deployment and affect performance. With network security policy management, automation allows security teams to apply changes instantly. This means businesses can launch promotions without delays. Another example involves cloud migration. Many businesses move workloads to cloud platforms in 2026. Automation ensures firewall policies remain consistent across environments. This improves security and simplifies management. When Security Complexity Starts Slowing You Down Businesses often realize they need automation when Firewall requests increase frequently Security teams spend too much time on manual tasks. Compliance requirements become stricter. Network infrastructure expands In these situations, network policy change automation becomes essential. It helps teams focus on strategic tasks instead of repetitive updates. Operational Benefits beyond Cost Savings Automation improves more than just operational costs. It enhances efficiency and reliability. Key benefits include Faster application deployment Improved security visibility Reduced human errors Better compliance management Stronger collaboration across teams With effective network security management, businesses can scale operations confidently while maintaining security standards. How to Choose the Right Automation Strategy Selecting the right automation solution requires careful evaluation. Businesses should consider Multi-vendor compatibility Integration with existing tools Workflow customisation options Reporting and compliance features Scalability for future growth Many businesses start with a phased approach. They automate high-priority policies first and gradually expand automation. The Future of Network Security Management Security operations in 2026 focus on speed, intelligence, and automation. Network security policy management enables organisations to adapt quickly while maintaining control. For example, businesses using hybrid environments rely on automation to maintain consistent policies. This approach reduces risks and improves operational efficiency. As security demands grow, network policy change automation will continue to transform how organisations manage infrastructure. Final Thoughts Security operations are becoming more complex, but automation offers a smarter path forward. With firewall rule change management and network security management, businesses can improve efficiency, reduce risks, and scale confidently. If you are ready to modernise your security operations, explore advanced automation solutions at Opinnate. Discover how intelligent network security policy management can simplify your infrastructure and help your team focus on growth. Frequently Asked Questions 1. What is network policy change automation? Network policy change automation helps organisations automate firewall rule updates and security policy changes across systems. 2. Why is firewall rule change management important? It ensures consistent security configurations and reduces manual errors in firewall updates. 3. How does network security policy management help businesses? It improves visibility, enhances compliance, and simplifies security operations. 4. When should businesses adopt network security management automation? Businesses should consider automation when network complexity increases and manual updates become time-consuming. 5. Is network policy change automation suitable for small businesses? Yes, even small businesses benefit from improved efficiency, faster updates, and stronger security.
Why Network Policy Change Automation is the Key to Faster Compliance and Audit Readiness

In the quickly changing digital world of today, companies that handle sensitive data, cater to regulated sectors, or run extensive corporate networks cannot compromise on maintaining compliance and making sure they are audit-ready. This work becomes more difficult due to the complexity of today’s IT infrastructures. The Network Policy Change Automation is one of the best tactics businesses are using to stay up to date. This robust solution not only optimizes operational processes but also greatly improves a business’s capacity to promptly, precisely, and without sacrificing network security to satisfy regulatory requirements and audit requirements. The Modern Solution: Automation Automating changes to network policies tackles these issues at their source. The formulation, approval, implementation, and documenting of policy changes may all be automated, which helps firms cut down on errors and minimize manual inefficiencies. Rather than depending on several teams to coordinate changes via old ticketing systems or protracted email chains, automation enables modifications to be carried out accurately and swiftly by pre-established rules and policy templates. In addition to security, this consistency is essential for keeping an audit trail that is transparent and verifiable. The Difficulty of Compliance in Contemporary Networks Regulations that organizations must comply with are becoming more numerous and include PCI-DSS, SOX, GDPR, and HIPAA. According to these rules, companies must manage who, what, and when can use their networks. Any configuration error or postponement of a policy change might result in non-compliance, severe fines, or harm to one’s reputation. The issue is that manual updates, ticketing systems, and compartmentalized change approval procedures—traditional approaches to managing network policy changes—cannot keep up with the speed and volume needed today. The slowness, inaccuracy, and bottlenecks caused by these approaches have a direct effect on compliance initiatives. Cutting Down on Risk in a Complicated Setting Human mistakes might result from any manual policy modification; an obsolete rule, an improper port, or an unintentional authorization could jeopardize the network’s security posture. In addition to causing security flaws, these mistakes also contravene both internal and external legislation. Because automation accurately enforces policy norms, it lowers this risk. It guarantees that every modification is thoroughly recorded and that only allowed and approved modifications are made. In settings where hundreds of policy revisions may take place every week, this degree of accuracy is crucial. Quicker Cooperation with Control and Reliability Having policies in place is not enough to be audit-ready; you also need to be able to show that they are routinely followed. Automated solutions guarantee that every modification to a network policy, from risk assessment to implementation, adheres to a defined procedure. This consistency reduces the time and effort needed for compliance assessments by making it simpler to provide the reports and logs auditors want. Additionally, visibility and control are provided via network policy change automation. In real-time, automated systems are able to detect misconfigurations, duplicate rules, and policy infractions. Companies may keep ahead of audit requirements by using this proactive strategy, which stops problems from becoming more serious and leading to regulatory failures. Opinnate’s Approach to Network Policy Automation Opinnate understands that audit readiness and compliance are not only IT concerns but also business needs. Our software offers full network visibility and administration while smartly and safely automating policy updates. We equip companies to save operational expenses, speed up compliance processes, and respond quickly to changing regulatory needs. Our solution ensures that security regulations are consistently consistent, enforceable, and audit-friendly by streamlining complex processes and facilitating seamless interaction with existing systems. Opinnate assists you in remaining confidently prepared for both internal governance and external audits. Developing a Compliance Plan for the Future Enterprise networks will face ever-increasing demands. Manual approaches will continue to fail due to increased complexity, dangers, and laws. Businesses must use automation to create a continuous, effective, and robust compliance posture. Network policy change automation has become a must, not a choice. Teams may now concentrate on strategic projects instead of battling configuration errors or rushing to get ready for audits. Moreover, it guarantees that your company is constantly prepared to demonstrate compliance, regardless of how the regulatory environment changes. Providing Assistance for Scalable and Agile IT Operations It is harder to manage policy changes across several environments as businesses embrace hybrid and multi-cloud architectures. Automation offers the scalability needed to effectively manage these dynamic systems. Instead of creating distinct procedures for cloud platforms, containerized environments, or on-premises systems, a single network policy change automation framework allows for unified administration. For enterprises hoping to enable innovation and corporate expansion while maintaining compliance, this flexibility is essential. Final Remarks In a time of intense regulatory scrutiny and constant cyber threats, automation provides a clear way ahead. Network policy change automation equips businesses with the means to confidently manage complexity, reduce risk, and uphold ongoing compliance. At Opinnate, we provide clever solutions that are adapted to the current network environment to assist companies in undergoing this transition. The moment to automate is now if you want rapid compliance and audit ready.
Firewall Rule Review Automation Need

Firewalls in today’s advanced and ever-changing network environments do not only act as security tools, but they provide the most important barrier of preventing cyber attacks. However, keeping an updated and productive firewall policy is easier said than done. Security teams almost always have a hard time managing and assessing firewall setups. This is mainly because there could be hundreds and sometimes thousands of rules. This is where firewall rule review automation comes in – a solution aimed at improving the efficiency with which firewall rule reviews are done, thereby enhancing security and ease of operations. In this article, we shall discuss the process of firewall rule review automation, its advantages and the reason why most organizations today find it mandatory in order to protect themselves from a plethora of threats. What Is Firewall Rule Review Automation? Firewall rule review automation is the process of evaluating firewall rule sets with the help of automated systems and tools. These systems and tools check the current rule set for repetitions, non-compliant config, un-optimized rule sets etc. Instead of having to visually search through, cross-reference, and manually keep inspired thousands of firewall rules (which is naturally slow, inexact, and needs a lot of manpower), there is little difficulty for an organization to deal with regimented processes of repeating firewall rule cleanups. Automation tools can identify discrepancies and suggest changes and also make sure that the policies of the firewalls are in accordance with the industry standards of practice and the regulations set out. The Difficulties of Manually Verifying Firewall Policies Although they are critical, many companies still use a manual method in reviewing and improving on the firewalls in place. Unfortunately, this kind of approach has a number of hurdles to overcome: Time-Consuming: Scanning through hundreds or even thousands of firewall rules is an arduous and time-consuming undertaking due to the manual process involved. Network security teams often take days if not weeks, just to complete one cycle of review. Human Limitations: No matter the level of skill and experience, manual evaluations will always have short comings. Some significant rules may be missed while some unnecessary ones may be present thus creating loopholes in security. Absence of Continuous Evaluation: In case of manual processing, escalation is also not feasible along with evaluation and implementation of the rules on a constant basis. There is no action until the damage has already occurred. Scaling Challenges: Organizations change, and changes in their networks are to be expected as well. Over time, it becomes too challenging and unsustainable to manually handle increasing firewall rules. The Need for Automation in Firewall Rule Reviews Given these challenges, it’s no surprise that firewall rule review automation is rapidly gaining traction. By automating rule reviews, organizations can reduce the workload on IT and security teams, minimize human error, and improve overall network security. Automation tools utilize algorithms and machine learning to analyze firewall rules, detect misconfigurations, and recommend optimizations. These tools can integrate directly into existing network infrastructures, providing continuous monitoring and proactive remediation of rule-related issues. Some of the Top Benefits of Automating the Firewall Rule Review. Let us consider a few of the advantages that can be explained through automation: Speed and Efficiency: One of the most significant advantages of automating firewall rule reviews is the speed with which they can be executed. What took weeks and months to accomplish can now be done within a few minutes. Using automated tools, it is possible to scan, analyze and optimize large rule sets within seconds allowing the organization to see the security status of the network in real-time. Reduction in Human Error: Automated systems eliminate the possibilities of human oversights. Advanced algorithms can identify anomalies as small as imperfect configurations, unneeded policies, or even security weaknesses that could easily be overlooked in a manual assessment. Continuous Monitoring and Real-Time Alerts: Automation tools, such as firewall rule review tools also issue alerts as soon as they observe or predict any risk or even configuration mistakes. This continuous alerting helps to ensure that the firewall system is always at peak performance which in turn reduces the level of risk posed by threats. Enhanced Compliance: It has now become less of a headache to ensure that the firewall settings maintain the set standards by authorities and the industry in general. Such tasks as carrying out compliance report assessments, auditing compliance with security policies and changes, and enforcement of security policies are easily accomplished using automation now. Cost Efficiency: Organizations can cut down the operating expense as operational cost is more at the time of manual cost when manual reviews are cut down. This gives IT teams the chance to devote more energy to other strategic activities instead of engaging in the tiresome process of several reviews of firewall rules. Furthermore, because of preventing disarray and breach of security, already the cost of automation is less due to avoided losses from downtime or clean-up costs. Better Scalability: As your business grows, your network infrastructure will inevitably become more complex. Automated rule review systems can easily scale alongside your infrastructure, ensuring that your security posture remains strong regardless of the size of your network. How to Implement Firewall Rule Review Automation Now that we understand the benefits, how can organizations begin to implement firewall rule review automation? Here are a few key steps: Firewall rule review automation is transforming how organizations approach network security. By automating the review process, businesses can save time, reduce human error, and maintain a strong security posture in an increasingly complex digital world. In the face of growing cyber threats and regulatory demands, automation is no longer a luxury but a necessity. By embracing automation, organizations can ensure that their firewalls remain an effective line of defense, safeguarding their data, systems, and reputations from the ever-present threat of cyberattacks.
Automated Firewall Rule Cleanup and Optimizing Firewalls

As effective against cyber-terrorism as any other component of the security apparatus, firewalls have become a traditional staple of contemporary networked systems. Firewalls control the incoming and outgoing traffic to and from a network by serving as a physical division between a ‘trusted’ internal network and an ‘untrusted’ outside network. With time and as the business evolves the size of the firm grows massive changes in the organization tend to affect the internal firewall rule base in that they get filled with old redundant extreme or excessive rules. So, automated firewall rule cleanup which helps in improving the overall performance of the network and protecting the network from external threats thereby optimizing firewall becomes is of great importance. One of the effective ways to increase performance and security of the firewall is doing automatic cleanup of the firewall rules. In this post, we’ll look into how automated firewall rule cleaning enhances firewall service making security risks less alarming, networks more efficient and ease their management. What is Automated Firewall Rule Cleaning? This involves the application of some software solutions which can clean excessive, unneeded, outdated or misconfigured rules from a firewall in relation to its present security or operational requirements. The marketing process usually has several steps and in most cases, these clean-up steps will include the following cleaning up of the rule base including: Finding redundant or unutilized rules: These types of rules tend to be rule bases which do not match with any current traffic since the scenarios for which such rules were built no longer exists, or new rules have superseded them.Streamlining conflicting or redundant rules: Usually, as rule bases expand, new updates on rules may include those that conflict or are similar with previous ones causing risks and or ineffective operations.Perfecting the sequence of rules: Rules have to be looked at in order since they are performed in a linear fashion, and the way the rules are ordered affects how well the firewall works. The purpose of rule optimization is to process heavy used rules first to reduce latency. Eliminating shadowed or overly permissive rules: These are rules that allow more access than necessary, increasing the attack surface, or rules that are “shadowed” by higher-priority rules, rendering them ineffective. By automating this cleanup process, organizations can ensure their firewalls operate efficiently without the need for manual intervention, which can be both time-consuming and error-prone. The Importance of Cleanup of Firewall Rules Firewalls are the primary mechanism used to restrict unauthorized access and are therefore used to protect a network from outside and inside threats. In most cases, however, due to the introduction of new applications, users, services, etc, to the cache, there are many existing rules which firewalls use, and this can quickly spiral out of control. This is how embargo usefulness of firewall rule cleanup comes into play. Rule bloat: Firewalls for example become loaded with hundreds if not thousands of rules, most of which are outdated and not relevant. Rule bloat can contribute to ineffeiciency in processing of the firewall thereby causing latency issues as the processing power of the firewall gradually settles over time with the associated increase in the number of deployed rules.Security threats: Proliferation of unneeded rules or the rules that are no longer relevant can pose a threat to security. These rules can allow attackers to circumvent security measures or simply increase the level of risk of attack towards the networks.Difficulty in management : Network managers who need to implement and monitor firewall policies will find it even more difficult in the presence of a disorganized rulebase. This excessive complexity gives rise to the chances of configuration mistakes which will compromise the security of the network.Compliance risks : Certain rules will apply to organizations in certain sectors due to their maximum risk investigated and their potential losses. Rule bloat and old configurations can hamper the audit process to keep up with regulations, compliance, and provide relevant updated parenting policies to respective stakeholders. To summarize, automated firewall rule cleanup must be carried out in order to achieve the intended protection of the network and enhancement of the performance of the firewall. The Link Between Automated Firewall Rule Cleanup and Firewall Optimization Firewall optimization is the process of improving the firewall’s performance, scalability, and security by refining the rule base, reducing processing time, and ensuring rules are accurate and effective. Automated firewall rule cleanup plays a critical role in this optimization by addressing the inefficiencies caused by rule bloat and configuration errors. 1. Enhanced Performance and Efficiency The more rules a firewall has, the longer it takes to process each packet of data. This results in latency, which can slow down the entire network, especially when firewalls have to inspect traffic for compliance with thousands of rules. Automated firewall rule cleanup removes unnecessary or outdated rules, reducing the total number of rules that need to be processed. This streamlines the inspection process and speeds up data transmission, leading to better overall network performance. Automated cleanup tools also ensure that rules are prioritized appropriately. Frequently used rules are positioned at the top of the rule base, ensuring that the firewall processes them first, thereby reducing the overall processing time. This kind of optimization ensures that the firewall operates efficiently even as traffic volumes grow. 2. Improved Security Posture A cluttered rule base can create significant security risks, as outdated rules may inadvertently allow unauthorized access or expose the network to vulnerabilities. Automated firewall rule cleanup eliminates redundant or obsolete rules, reducing the attack surface and closing potential security gaps. For example, overly permissive rules that allow access to a broader range of IP addresses or ports than necessary are common culprits of security breaches. Automated tools can identify these rules and either tighten their permissions or remove them entirely, ensuring that only authorized traffic is permitted. Additionally, automated cleanup tools provide better visibility into rule usage, helping administrators quickly identify security risks or conflicts within the rule base. This allows for faster remediation of vulnerabilities and
Firewall Security Orchestration and its Effect on the Security

With the continuously changing trends and developments within the digital space, the security of the enterprise networks has ranked among the most important factors than it has ever been before. Cyber attacks are more sophisticated nowadays that the past ways of managing the firewalls have been rendered futile. Thanks to firewall security orchestration strategies that provide a more intelligent and automated way of managing firewalls that greatly improves the security levels generally. This post will outline the significance of firewall security orchestration and its effect on the security of the organization, helping companies fighting against cyber-attacks. What Is Firewall Security Orchestration? Simply put firewall security orchestration is the choreography of different security processes across different firewall systems in an automated way. Now, rather than having to set up a firewall by hand, security orchestration platforms enable the functional deployment, overseeing, and operation of a network of firewalls. This makes it easier for businesses to aggregate their cloud flame walls management including data cesntered evironments, cloud instances and even virtualized layers. There are two things that are important to note here. First, that a well-orchestrated firewall security system takes away the drudgery and often complicated very long processes of managing firewall rules, configurations and policy updates. Secondly and more important is that firewalls so orchestrated make it possible for a security team’s operations in countering any threats to be greatly reduced in time due to the fact operations such as threat detection, incdent response as well as remediation are all automated thereby cutting down chances of human error that could lead to operational inefficiencies. How Firewall Orchestration Enhances Overall Security 1. Centralized Management and Visibility One of the key benefits of firewall orchestration is centralized management. Orchestration platforms provide a single-pane-of-glass view into all firewall systems, whether they are deployed in a traditional data center, in the cloud, or in hybrid environments. This centralization enhances visibility into all firewall policies and configurations across the network, giving security teams a comprehensive understanding of their organization’s security posture. By having a holistic view of the firewall infrastructure, security professionals can easily identify potential vulnerabilities and conflicts in firewall rules. Moreover, having a centralized dashboard makes it easier to enforce consistent security policies across all firewalls, reducing the chances of human error or policy drift. 2. Automation of Repetitive Tasks One of the biggest challenges in firewall management is the sheer volume of repetitive tasks. These can include rule creation, policy updates, logging, and monitoring traffic patterns. Traditionally, these tasks would be done manually, leading to a higher risk of misconfigurations and inconsistent application of rules across different environments. Firewall security orchestration automates these processes, ensuring consistency in rule application and reducing the time it takes to deploy changes. Automation helps security teams stay agile, respond to threats in real-time, and proactively manage potential vulnerabilities. 3. Reduced Human Error Human error is a significant cause of network security breaches, particularly when managing complex firewall infrastructures. Manually configuring rules, monitoring traffic, and responding to incidents across multiple firewalls can lead to mistakes that expose networks to cyber threats. By automating critical tasks through firewall security orchestration, the potential for human error is minimized. This reduces the likelihood of misconfigurations and policy violations that can result from manual processes. Furthermore, with orchestration tools in place, security teams can enforce change control processes, ensuring that any updates or modifications to firewall rules are thoroughly vetted and approved before implementation. 4. Faster Incident Response In the event of a security breach, time is of the essence. Manual responses to incidents, such as identifying and mitigating threats, can take hours or even days—time that cybercriminals can exploit to cause significant damage. Firewall security orchestration accelerates incident response by automating the identification, isolation, and remediation of threats. For instance, if a suspicious pattern of traffic is detected, the orchestration platform can automatically block that traffic and update firewall rules to prevent further incidents. This rapid response minimizes the potential impact of attacks and helps organizations stay resilient in the face of cyber threats. 5. Compliance and Audit Readiness Many industries are governed by strict regulations that mandate compliance with security standards, such as GDPR, HIPAA, and PCI DSS. Compliance often requires organizations to demonstrate that they have appropriate security controls in place, including robust firewall policies. Firewall security orchestration makes it easier to ensure compliance by providing automatic documentation of firewall rules and policies. The orchestration platform can generate audit-ready reports that detail the security measures in place, helping organizations meet regulatory requirements and avoid costly fines. Additionally, the ability to automate compliance checks ensures that firewall rules are always aligned with regulatory guidelines. The Business Advantages of Using Orchestration of Firewall Security The deployment of firewall security orchestration does not just improve security levels, it has business advantages as well. Such advantages include: Operational Cost Reduction: Organizations can carry out firewall management in a self-sufficient manner and avoid the manual processes. This reduces operational costs and enables the security teams to focus on more strategic initiatives. Enhancement of Efficiency: With automation, the burden on the IT and security officers is considerably reduced thereby allowing them to engage more on threat hunting and incident response than doing mundane tasks like updating firewall rules. Ability to Grow with the Business Environmental Changes: With the expansion of a business, the network infrastructure is also expanded. Firewall security orchestration ensures that the application of security policies is elongated across several environments without causing additional complications. Enhancing the Defense Architecture through the Firewall Security Orchestration In these days of advanced cyber warfare tactics, the use of a firewall employing a manual process, cannot be relied upon to defend a company’s critical information. Firewall security orchestration attempts to resolve this challenge by providing useful automation of firewall processes and considerable reduction in the reliance on people as well as faster response to threats. With the implementation of the firewall security orchestration, organizations will be looking at not only increasing their security levels but also
Firewall Policy Automation Tools: Unlocking Efficiency

For most firms today, configuring and managing firewall policies without the assistance of tools and solutions is an impossible idea. With the advent of cloud systems, upsurge in the number of connected devices, and multi-dimensionality of network structures involve more solutions that are advanced and optimized in every aspect than these policies. And so comes the role of firewall policy automation tools. These devices not only reduce the burden of operation of firewall policies but also guarantee that there is order in the enforcement of security measures within complicated network systems, mitigating the chances of mistakes occurring due to human factors. In this post, we will focus on the meaning of firewall policy automation tools, their importance in current businesses, and the impact these tools will have in the management of network security in companies. What Are Firewall Policy Automation Tools? Firewall policy automation tools are software applications that control the processes of adding, altering, and enforcing rules that govern the use of the firewall in the network of organisations. Such tools are capable of executing a rather complex policy management function of producing, deploying and monitoring adherence to manifest organizational security policies even in the presence of traffic typical to networks. Major Inclusions in Firewall Policy Automation Tools: Rule Lifecycle Management: Help organizations manage a range of firewall rule processes including design, approval, implementation, and removal. Audit and Compliance: The given tools also track the history and progression of users of firewall systems with respect to the policies in enforcement helping to meet requirements of standards such as that of GDPR, HIPAA or PCI DSS. Centralized Management: Such automation systems allow for a one stop construction or modification of extant and new firewall policies across multiple vendors and devices, eliminating the need to manually configure policies for each firewall in a heterogeneous environment Traffic Analysis: Modern automation tools analyze network traffic patterns to suggest optimal firewall policies. This not only enhances security but also improves network performance by reducing the number of redundant or conflicting rules. Risk Analysis: Automated tools often come with built-in risk assessment features, which evaluate the security implications of each firewall rule before it’s implemented. This helps organizations avoid the common pitfall of misconfigured firewall rules that create security vulnerabilities. Change Management: Integrated change management features ensure that firewall rule modifications are reviewed, approved, and tracked, minimizing the risk of unauthorized changes and simplifying auditing processes. Why Are Firewall Policy Automation Tools Important? Manual firewall rule management is not only time-consuming but also prone to human error. As enterprise networks grow in complexity, managing thousands of firewall rules across multiple firewalls becomes a daunting task. Even a small error in a firewall rule can expose the network to security breaches, cause performance bottlenecks, or create compliance issues. Here’s why firewall policy automation tools are critical for modern enterprises: 1. Increased Security Manually managing firewall rules is not scalable. Automation tools continuously monitor network traffic and adjust firewall rules as necessary, ensuring that security policies are always up-to-date. Additionally, the risk analysis features available in many firewall policy automation tools reduce the likelihood of misconfigurations that could lead to vulnerabilities. 2. Improved Compliance For organizations in regulated industries, maintaining compliance is a top priority. Automated tools generate reports on firewall rule changes and can automatically alert administrators to any rule violations or misconfigurations. This makes audits significantly easier and reduces the risk of non-compliance. 3. Operational Efficiency Automating firewall rule management allows IT teams to focus on more strategic initiatives rather than spending countless hours manually configuring and managing firewall policies. Automation also reduces the turnaround time for deploying new rules, speeding up response times for security incidents. 4. Reduced Costs Reducing the time spent on manual configurations and minimizing errors helps organizations cut operational costs. Furthermore, automation tools ensure that resources are used efficiently by avoiding redundant or outdated firewall rules that could lead to unnecessary network congestion. 5. Scalability As networks grow in size and complexity, so does the number of firewall rules that need to be managed. Automation tools scale with the network, ensuring that security policies remain consistent even as new devices or networks are added. Top Considerations When Choosing a Firewall Policy Automation Tool Selecting the right firewall policy automation tool for your organization can be a challenge, given the number of solutions on the market. Here are a few key factors to consider: 1. Vendor Compatibility Ensure the tool supports firewalls from multiple vendors, especially if your organization uses a mix of firewall solutions. A good automation tool will allow you to manage all your firewalls from a centralized platform. 2. User-Friendly Interface An intuitive and easy-to-use interface is essential for ensuring that even non-technical team members can manage and configure firewall rules without difficulty. The user experience can make or break the adoption of an automation tool. 3. Customizability The ability to customize rules and policies to fit your organization’s unique needs is crucial. Look for a tool that offers flexibility in creating, modifying, and enforcing rules while maintaining compliance with security standards. 4. Reporting and Analytics Comprehensive reporting and analytics features are essential for monitoring firewall rule performance, identifying potential issues, and ensuring compliance with regulations. These insights allow for more proactive management of network security. 5. Risk and Compliance Management Some firewall policy automation tools offer built-in risk assessment and compliance management features. This ensures that all firewall rule changes are in line with your organization’s security posture and regulatory requirements. How will firewall policy management evolve in the future? The advancement of automation tools has led to the addition of AI and ML in many of them. This helps in revolutionizing alert- dialer policy automation tools. They will be able to predict- from analyzing the network traffic- change certain rules in the firewall issue plastic based on a model with automation. This will not only increase security but also enhance and expand the influence of firewall control. How Opinnate Can Help In case you
The Role of NSPM in Network Security Automation: A Must-Have for Modern Enterprises

NSPM enhances network security’s automation. It has become an integral part of most enterprises.The cybersecurity sector is a continuous turnover and undoubtedly, Building and maintaining a secure network would be a hard nut to crack. It is because, as companies advance and the networks increase in size, the enforcement of the security governance policies defeats the purpose. To rise to this challenge, a good number of firms are seeking the help of network security automation, which is defined as the innovative use of modern tools to simplify, implement, and manage the security policies of broad and often complex IT environments. Network Security Policy Management (NSPM) is a process that stands central in network security automation. It is an important solution that ensures the security policies are well-governed, do not compromise on compliance and are always in place irrespective of the threat challenges. This article defines what is network security automation and goes further to discuss why it is vital for the organizations and how the news about NSPM solutions is changing this vital trend making it an astute weapon for the organizations aiming at securing their information. What is Network Security Automation? Automating network security management entails automating the processes of implementing, maintaining, and controlling security policy across the entire network. It makes it possible to manage human labour more efficiently and improve the speed of response to possible threats thereby enhancing the network. In a classical approach of security management, it is the responsibility of the network administrator to configure access lists, firewalls and other security measures. This approach is slow, error-prone and simply does not work in any effective way in the rapidly changing, cloud based world. By the use of automation, organizations are able to execute these processes in a simplified manner thus making it possible to have systems that are secure but at the same time easy to transform and incorporate new risks and infrastructure changes. The Role of NSPM in Network Security Automation Network Security Policy Management (NSPM) plays a central role in network security automation by serving as the core solution that integrates, automates, and manages security policies across the entire network. NSPM solutions provide visibility, control, and automation of security policies across diverse environments, ensuring that the network remains secure and compliant with regulatory standards. Here’s how NSPM contributes to network security automation: 1. Centralized Management of Security Policies One of the main benefits of NSPM is the centralization of security policy management. In modern networks, organizations often use multiple firewalls, routers, switches, and cloud infrastructures. Without a centralized system, managing security policies across these different devices and platforms becomes overwhelming and leads to inconsistencies. NSPM automates the process by providing a unified platform where all security policies can be managed, monitored, and updated from a single interface. This ensures that all devices across the network follow the same security rules, reducing the chances of misconfigurations and security gaps. 2. Policy Consistency and Automation Across Hybrid Environments Most organizations today operate in hybrid environments that combine on-premises systems, public clouds, and private clouds. Maintaining consistent security policies across these varied environments is a significant challenge, especially when done manually. NSPM solutions automate the application of security policies across hybrid environments, ensuring that policies are consistent and compliant with internal and external regulations. This consistency is critical in preventing security lapses as traffic moves between different environments. Additionally, NSPM can detect policy conflicts and automatically resolve them, preventing configuration issues that could expose the network to vulnerabilities. 3. Improved Threat Response and Mitigation Cyberattacks are becoming more sophisticated and frequent, making it essential for organizations to respond quickly to threats. Manual processes slow down incident response times, as IT teams need to assess the issue, locate the vulnerable policy, and manually apply a fix. NSPM solutions help automate the threat detection and response process. When a threat is detected, NSPM can automatically apply predefined security policies to mitigate the issue. For example, if a vulnerability is found in a particular part of the network, NSPM can automatically block access to that segment, limiting potential damage until the threat is neutralized. This rapid response capability is crucial in minimizing the impact of cyberattacks. 4. Reducing Human Error Through Automation Human error remains one of the leading causes of security breaches. Manual processes are inherently prone to mistakes—misconfigurations, overlooked updates, or even incorrect rule implementation can open up critical vulnerabilities in the network. With NSPM, these manual tasks are automated, significantly reducing the risk of human error. Whether it’s updating firewall rules, configuring access control, or implementing new security policies, NSPM ensures these actions are performed accurately and consistently. By automating these tasks, security teams can spend more time focusing on strategic priorities, like threat analysis and incident response, rather than being bogged down by routine configuration tasks. 5. Enhanced Visibility and Reporting Visibility is a key element of network security automation. Without full visibility into the network, it’s impossible to know whether security policies are being followed, whether there are any gaps, or how data is flowing through the system. NSPM solutions provide detailed, real-time visibility into the entire network infrastructure, enabling security teams to monitor the effectiveness of security policies, detect anomalies, and perform audits more easily. NSPM tools typically come with advanced reporting features that automate compliance checks and generate detailed reports on policy enforcement and network security status. These reports help organizations meet regulatory requirements while maintaining high standards of security. 6. Ensuring Compliance with Regulatory Standards Regulatory compliance is a critical concern for businesses across industries, particularly those dealing with sensitive customer data or operating in highly regulated sectors like finance or healthcare. Manually ensuring that network security policies comply with industry standards (such as GDPR, HIPAA, or PCI-DSS) can be daunting and error-prone. NSPM solutions automate compliance management by continuously monitoring the network for any deviations from regulatory requirements and automatically updating policies to stay in line with the latest standards. This ensures that organizations can maintain compliance without
Network Policy Orchestration: Enhancing Firewall Management
The need for robust firewall management has become paramount. With the proliferation of cyber threats, organizations face the daunting task of ensuring that their network security measures remain effective, efficient, and adaptable. Enter Network Policy Orchestration (NPO), a revolutionary approach to firewall management that streamlines policy creation, enforcement, and monitoring. In this blog post, we delve into the intricacies of NPO, its importance, use cases, and advantages in modern cybersecurity frameworks. Understanding Network Policy Orchestration Network Policy Orchestration refers to the centralized management and automation of network security policies across heterogeneous environments. It encompasses the creation, modification, enforcement, and monitoring of firewall rules, ensuring consistent security posture across the network infrastructure. NPO solutions leverage automation and orchestration technologies to simplify complex policy management tasks, thereby enhancing operational efficiency and reducing the risk of human errors. Importance of Orchestration Effective firewall management is crucial for safeguarding sensitive data, mitigating cyber threats, and ensuring regulatory compliance. However, traditional manual approaches to policy management are often time-consuming, error-prone, and difficult to scale. NPO addresses these challenges by providing a unified platform for policy management, enabling organizations to enforce security policies consistently across diverse network environments. By automating routine tasks and streamlining policy workflows, NPO empowers organizations to respond swiftly to emerging threats and adapt their security posture in real-time. Use Cases of NPO Advantages of Network Policy Orchestration In an era marked by relentless cyber threats and digital transformation, Network Policy Orchestration emerges as a vital component of modern cybersecurity frameworks. By providing centralized management, automation, and real-time visibility, NPO empowers organizations to strengthen their firewall management practices, mitigate security risks, and adapt to evolving threat landscapes. As organizations continue to embrace digital innovation, the adoption of NPO will be instrumental in enhancing the resilience and agility of their cybersecurity posture. Network Policy Orchestration isn’t just a buzzword; it’s a strategic imperative for organizations striving to stay ahead in an increasingly complex and dynamic threat landscape. Embrace the power of NPO and take proactive steps towards fortifying your network defenses against emerging cyber threats.


