Navigating the Digital Peril: Safeguarding Against Cybersecurity Threats and Essential Precautions

In our technology-driven era, the digital landscape offers unprecedented opportunities for growth and connectivity. Yet, this landscape is also rife with potential hazards in the form of cyber threats that can wreak havoc on personal and organizational data. As the stakes continue to rise, understanding these threats and adopting crucial precautions becomes paramount. In this comprehensive guide, we’ll explore the dynamic realm of cybersecurity threats and unveil essential measures to fortify your digital defenses. Unveiling the Landscape of Cybersecurity Threats The cyber threat landscape is constantly evolving, with malicious actors employing innovative techniques to exploit vulnerabilities and gain unauthorized access. It’s crucial to comprehend the breadth of these threats to adequately prepare against them: Essential Precautions to Bolster Cybersecurity In the face of these multifaceted threats, taking proactive measures to safeguard your digital assets and sensitive information is non-negotiable. Here are crucial precautions that individuals and organizations should implement: 1. Keep Software Updated: Regularly update operating systems, applications, and security software to patch vulnerabilities. Attackers often target outdated software with known weaknesses. 2. Strong Password Practices: Implement robust password policies that encourage the use of complex passwords and multi-factor authentication (MFA). Change passwords periodically and never reuse them across accounts. 3. Security Awareness Training: Educate employees, contractors, and users about cybersecurity best practices. Training can help individuals recognize phishing attempts, social engineering tactics, and other threats. 4. Regular Data Backups: Frequently back up critical data to offline or secure cloud storage. This precaution can mitigate the impact of ransomware attacks and data loss incidents. 5. Network Segmentation: Segment your network into isolated zones, limiting lateral movement for attackers. This strategy can mitigate the spread of threats across your infrastructure. 6. Firewall and Intrusion Detection Systems: Deploy firewalls and intrusion detection systems (IDS) to monitor network traffic for suspicious activities. These tools can detect and prevent unauthorized access attempts. 7. Endpoint Security: Install and update antivirus software, anti-malware solutions, and endpoint detection and response (EDR) tools on all devices connected to your network. 8. Secure Web Browsing: Enable safe browsing features on web browsers to prevent users from visiting malicious websites. Additionally, utilize web filtering to block access to risky or inappropriate sites. 9. Incident Response Plan: Develop a comprehensive incident response plan outlining steps to take in the event of a cyber attack. Test the plan through simulated exercises to ensure its effectiveness. 10. Vendor Security Assessment: Assess the cybersecurity measures of third-party vendors and partners before sharing sensitive information or granting access to your network. 11. Encrypt Data: Implement encryption for sensitive data, both during transit and while at rest. Encryption adds an additional layer of protection against unauthorized access. 12. Regular Security Audits: Conduct periodic security audits to assess vulnerabilities, evaluate the effectiveness of existing measures, and identify areas for improvement. 13. Employee Vigilance: Encourage a culture of cybersecurity awareness among employees. Instill caution regarding email attachments, links, and requests for sensitive information. 14. Patch Management: Maintain a robust patch management strategy to ensure that all software and systems are up to date with the latest security patches. The Path to a More Secure Digital Future As cyber threats grow in complexity and frequency, adopting a proactive stance in cybersecurity is no longer optional – it’s imperative. By understanding the diverse range of threats and implementing the essential precautions outlined above, individuals and organizations can fortify their digital defenses and mitigate the risks posed by malicious actors. Remember, cybersecurity is a continuous effort. Regularly review and adapt your strategies to stay ahead of evolving threats. By embracing these precautions and fostering a culture of vigilance, you can navigate the digital landscape with confidence, knowing that you’ve taken significant steps to safeguard your digital assets and sensitive information.
Navigating the Digital Frontier: Understanding the Importance of Cybersecurity Reports

In an increasingly interconnected world, where digital footprints are the norm and data breaches are a grim reality, the role of cybersecurity has become paramount. As organizations and individuals alike grapple with the ever-evolving threat landscape, cybersecurity reports emerge as vital tools for understanding, mitigating, and responding to cyber risks. In this blog post, we delve into the significance of cybersecurity reports, their components, and their role in shaping a secure digital future. The Cybersecurity Landscape: Why Reports Matter Cyber threats are no longer confined to the realms of science fiction; they’re a tangible threat to businesses and individuals alike. From data breaches that expose sensitive information to ransomware attacks that paralyze critical systems, the consequences of cyber incidents are far-reaching. Cybersecurity reports offer a window into this landscape, enabling organizations to make informed decisions to safeguard their digital assets. **1. Threat Awareness: Cybersecurity reports provide up-to-date information on the latest threats, attack vectors, and vulnerabilities. This knowledge empowers organizations to proactively identify potential risks and take preventive measures. **2. Benchmarking and Best Practices: Reports often include benchmark data and best practices for cybersecurity. By comparing their security posture with industry standards, organizations can identify gaps and areas for improvement. **3. Risk Management: Understanding the risks is the first step to managing them. Cybersecurity reports help organizations assess their risk exposure and allocate resources effectively to mitigate potential threats. **4. Incident Response: In the event of a cyber incident, having a robust incident response plan is critical. Cybersecurity reports offer insights into incident trends, helping organizations refine their response strategies. Components of a Comprehensive Cybersecurity Report A well-structured cybersecurity report encompasses various components that collectively offer a holistic view of the current threat landscape and effective countermeasures. **1. Executive Summary: A succinct overview of the report’s findings, tailored for non-technical stakeholders, providing a high-level understanding of the cybersecurity landscape. **2. Threat Intelligence: Detailed analysis of emerging threats, including malware trends, attack vectors, and vulnerabilities exploited by cybercriminals. **3. Incident Analysis: Insights into recent cyber incidents, including the nature of attacks, industries affected, and the impact of breaches. This section aids in understanding real-world consequences. **4. Vulnerability Assessment: An overview of existing vulnerabilities in software, systems, and applications, accompanied by recommended patches and updates. **5. Best Practices: Guidelines for strengthening cybersecurity measures, ranging from user training to network segmentation and encryption protocols. **6. Regulatory Compliance: Information on compliance requirements specific to industries, helping organizations stay within legal boundaries. **7. Case Studies: Real-world examples of successful cybersecurity implementations and lessons learned from incidents, offering practical insights. Tailoring Reports to Your Needs Every organization’s cybersecurity needs are unique, and thus, their approach to utilizing cybersecurity reports should be customized. **1. Industry Relevance: Seek reports that are tailored to your industry. Different sectors face distinct threats and regulations, making industry-specific insights invaluable. **2. Risk Profile: Assess your organization’s risk profile to determine which threats and vulnerabilities are most relevant. Focus on areas that pose the greatest risk to your operations. **3. Emerging Technologies: If your organization adopts emerging technologies like IoT or cloud computing, ensure that your chosen reports cover threats pertinent to these domains. **4. Continuous Learning: The cybersecurity landscape evolves rapidly. Regularly access new reports to stay updated on emerging threats and countermeasures. Leveraging Reports for Action While cybersecurity reports provide valuable insights, their true value lies in the actions they inspire. Here’s how organizations can leverage these reports effectively: **1. Risk Prioritization: Identify the most critical risks to your organization based on the report’s findings and allocate resources accordingly. **2. Policy Review: Use the report’s best practices section to evaluate and update your organization’s cybersecurity policies and procedures. **3. Incident Response Enhancement: Analyze case studies of cyber incidents to refine your organization’s incident response plan and minimize potential damage. **4. Employee Training: Utilize threat intelligence to educate employees about common attack vectors and how to recognize phishing attempts. **5. Stakeholder Communication: Share key insights from reports with executives and board members to garner support for cybersecurity initiatives. In a digital landscape fraught with cyber threats, knowledge is the most potent weapon. Cybersecurity reports bridge the gap between awareness and action, equipping organizations with the information needed to secure their digital assets effectively. By staying updated on emerging threats, best practices, and incident analyses, organizations can proactively enhance their security posture. As cybercriminals become more sophisticated, the role of cybersecurity reports will continue to grow, playing a crucial part in the collective effort to build a resilient and secure digital future.
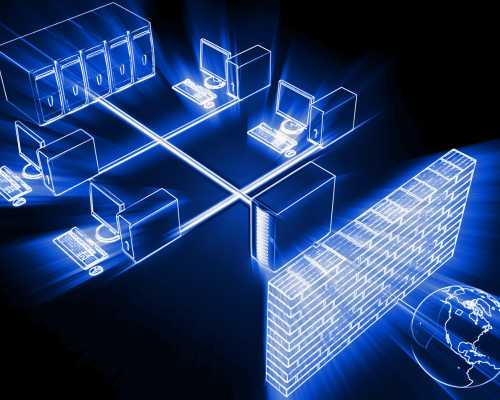
Enhancing Security Operations Centers: The Imperative of Firewall Automation and Network Security Policy Management (NSPM)

In today’s fast-paced digital landscape, organizations face an ever-evolving landscape of cyber threats. As attackers become more sophisticated, it’s imperative for businesses to fortify their cybersecurity measures. One of the key pillars in this defense strategy is the Security Operations Centers (SOC), a centralized unit responsible for monitoring, detecting, and responding to security incidents. To bolster SOC efficiency and effectiveness, Firewall Automation and Network Security Policy Management (NSPM) have emerged as indispensable tools. In this blog post, we’ll explore the critical role of these technologies in modern security operations. The Rise of Security Operations Centers (SOCs) In the face of relentless cyber threats, organizations have recognized the need for a dedicated unit to manage their cybersecurity. This is where Security Operations Centers come into play. SOC teams are responsible for monitoring networks, systems, and applications to identify and respond to potential security breaches. Their goal is to detect anomalies, investigate potential incidents, and coordinate timely responses to mitigate risks. However, the traditional manual methods of managing security policies and monitoring firewalls are becoming insufficient to combat today’s sophisticated threats. As networks grow more complex and attack surfaces expand, SOC teams require advanced tools to streamline their operations and maintain a robust security posture. The Need for Firewall Automation Firewalls serve as the first line of defense against unauthorized access and cyber threats. They regulate incoming and outgoing network traffic based on predefined security policies. Traditionally, managing firewall rules has been a manual and resource-intensive task, often prone to human errors. This is where firewall automation steps in. 1. Rapid Response to Threats: Automated firewall management enables SOC teams to swiftly respond to threats. When a potential security breach is detected, automation can trigger predefined actions, such as blocking suspicious IP addresses or isolating compromised systems. 2. Consistency and Compliance: Maintaining a consistent and compliant security posture across the organization can be challenging with manual rule management. Automation ensures that security policies are consistently applied and adhered to, reducing the risk of misconfigurations. 3. Efficient Resource Utilization: SOC teams are often inundated with alerts and incident data. Automating routine tasks like firewall rule changes frees up valuable human resources, allowing experts to focus on high-value tasks such as threat analysis and incident response. 4. Scalability: As organizations grow, managing a burgeoning number of firewall rules becomes arduous. Automation equips SOC teams to handle this scalability without sacrificing security or efficiency. 5. Error Minimization: Human errors in firewall rule configurations can lead to security vulnerabilities. Automation reduces these risks by following predefined logic and minimizing manual intervention. Network Security Policy Management (NSPM): A Strategic Asset While firewalls play a pivotal role in cybersecurity, their effectiveness is directly tied to the accuracy and relevance of network security policies. Network Security Policy Management(NSPM) is the discipline of designing, implementing, and maintaining these policies coherently across an organization’s network infrastructure. 1. Visibility and Control: NSPM provides SOC teams with a comprehensive view of the organization’s network security landscape. It helps identify inconsistencies, overlaps, and gaps in security policies, allowing for precise control over traffic flow. 2. Risk Reduction: Inadequate policy management can inadvertently expose critical assets or create unnecessary access paths. NSPM helps minimize these risks by enforcing the principle of least privilege and ensuring that policies align with business requirements. 3. Streamlined Compliance: Regulatory compliance is a significant concern for organizations across industries. NSPM simplifies the process of demonstrating compliance by providing documentation and audit trails of policy changes. 4. Adaptive Security: As business needs evolve, so do security requirements. NSPM enables SOC teams to adapt security policies to changing environments and emerging threats, ensuring a proactive defense strategy. 5. Collaboration and Efficiency: In large organizations, multiple teams may require access to different segments of the network. NSPM facilitates collaboration by allowing teams to define and manage their own policies while adhering to a centralized framework. Achieving Synergy: Firewall Automation and NSPM While firewall automation and NSPM offer distinct benefits, their true potential is realized when they work in harmony within a SOC environment. 1. Real-Time Threat Response: Integrating automation with NSPM enables real-time threat response. When a threat is detected, automated actions can be taken to modify firewall rules through NSPM, thereby containing the threat’s impact. 2. Adaptive Policy Enforcement: The dynamic nature of modern networks demands flexibility in security policies. By automating policy adjustments through NSPM, SOC teams can rapidly adapt to new attack vectors and network changes. 3. Continuous Compliance: Firewall rule changes can impact compliance. NSPM, when paired with automation, ensures that policy modifications are tracked, documented, and validated for compliance purposes. 4. Enhanced Analysis: Automation of routine tasks through NSPM frees up SOC personnel to focus on advanced threat analysis and strategic decision-making, ultimately strengthening the organization’s security posture. 5. Reduced Incident Dwell Time: By automating threat response processes, SOC teams can significantly reduce incident dwell time—the duration a threat remains undetected and active within the network. In conclusion, as cyber threats grow more sophisticated, Security Operations Centers need robust tools to effectively manage security policies and respond to incidents. Firewall automation and Network Security Policy Management provide the much-needed edge by improving response times, ensuring consistency, and enhancing overall security posture. Their integration empowers SOC teams to proactively address threats, maintain compliance, and make informed decisions in an ever-evolving threat landscape. As organizations continue to prioritize cybersecurity, embracing these technologies will become less of an option and more of a necessity for safeguarding sensitive data and digital assets.
Navigating the Digital Frontier: The Crucial Role of Firewalls in Ensuring a Secure Internet Experience

As cyber threats continue to evolve, ensuring a secure internet access experience has become paramount. At the forefront of this defense strategy is the firewall – a powerful guardian that plays a crucial role in safeguarding your digital presence. In this comprehensive guide, we explore the concept of a secure internet and delve into the pivotal role that firewalls play in achieving this goal. Understanding the Foundations of a Secure Internet A secure internet encompasses a digital environment where individuals and organizations can navigate, communicate, and conduct transactions without falling prey to cyber threats. Whether it’s personal data, sensitive business information, or confidential financial details, users need the assurance that their online interactions are shielded from malicious actors. A secure internet access is characterized by: The Role of Firewalls in Crafting a Secure Internet Landscape Among the arsenal of cybersecurity tools, firewalls stand as the sentinels that monitor and control incoming and outgoing network traffic. Acting as a barrier between trusted internal networks and external, potentially harmful sources, firewalls serve as the first line of defense against a diverse array of cyber threats. Here’s how firewalls contribute to a secure internet experience: 1. Traffic Inspection and Filtering: Firewalls meticulously examine network traffic, scrutinizing packets of data for signs of malicious activity. This inspection includes analyzing source and destination addresses, as well as checking for unauthorized access attempts or suspicious patterns. By filtering out potentially harmful traffic, firewalls prevent cybercriminals from gaining access to your network. 2. Access Control: Firewalls enforce access controls by setting rules that determine which types of traffic are permitted to enter or leave a network. These rules can be tailored to specific IP addresses, applications, or services, providing a granular level of control. By limiting access to only authorized parties, firewalls thwart unauthorized entry and prevent data breaches. 3. Intrusion Detection and Prevention: Firewalls are equipped with intrusion detection and prevention capabilities that identify and thwart malicious activities in real time. When a firewall detects suspicious behavior, such as repeated failed login attempts or patterns consistent with a cyberattack, it can take immediate action to block the threat and alert administrators. 4. Application Layer Security: Modern firewalls extend their protection to the application layer, scrutinizing the data exchanged between applications and users. This safeguards against attacks that exploit vulnerabilities in software or web applications, helping prevent data leaks and unauthorized access. 5. Content Filtering: Firewalls can be configured to filter out specific types of content, such as malicious websites, malware, or inappropriate content. This feature is particularly valuable for organizations that want to ensure a safe and productive internet experience for their employees while minimizing the risk of cyber threats. 6. Virtual Private Networks (VPNs): Firewalls often include VPN capabilities, allowing users to establish secure connections to remote networks. This is especially useful for remote workers or individuals accessing public Wi-Fi networks, as VPNs encrypt data traffic, protecting it from potential eavesdropping. 7. Logging and Reporting: Firewalls maintain detailed logs of network activities, which can be analyzed to identify trends, potential threats, and areas for improvement. These logs also play a crucial role in post-incident analysis, helping organizations understand the nature of security breaches and refine their defense strategies. Implementing an Effective Firewall Strategy for a Secure Internet To fully leverage the protective capabilities of firewalls and create a secure internet access experience, organizations and individuals need to follow a strategic approach: 1. Choose the Right Firewall: Select a firewall solution that aligns with your security needs and network infrastructure. Whether hardware-based or software-based, ensure that the firewall offers the features required to defend against your specific threat landscape. 2. Configure Rules Carefully: Configure firewall rules based on your organization’s security policies and requirements. Establish rules that prioritize business-critical applications, services, and communications while blocking unauthorized or malicious traffic. 3. Regular Updates: Keep your firewall’s firmware and software up to date to ensure that it can effectively combat emerging threats. Cybercriminals are constantly devising new tactics, so timely updates are crucial to maintaining robust security. 4. Continuous Monitoring: Regularly monitor your firewall’s logs and reports to identify any anomalies or potential security breaches. Promptly investigate and respond to any suspicious activity. 5. Employee Education: Educate employees and users about safe internet practices and the importance of adhering to security protocols. A well-informed workforce can help mitigate the risk of social engineering attacks that attempt to bypass firewalls. 6. Regular Audits: Conduct periodic audits to evaluate the effectiveness of your firewall strategy. Identify areas for improvement and adjust your configuration based on changing threats or business requirements. In the digital age, a secure internet experience is a fundamental requirement for individuals and organizations alike. Firewalls stand as stalwart guardians, leveraging their traffic inspection, access control, and intrusion prevention capabilities to create a fortified barrier against cyber threats. By implementing an effective firewall strategy and staying vigilant against evolving dangers, we can navigate the digital landscape with confidence, knowing that our online interactions are shielded by the watchful eye of these cybersecurity sentinels.
Defending Against Evolving Network Security Threats: Strategies for Effective Protection
In an increasingly interconnected world, where digital landscapes drive business operations, network security has taken center stage. The reliance on networks for communication, data exchange, and operations has also attracted a multitude of cyber threats that continue to evolve in complexity. To safeguard sensitive information and maintain business continuity, organizations must remain vigilant and proactive in combating network security threats. In this article, we will delve into the realm of network security threats and explore effective strategies for combating them. Understanding Network Security Threats Network security threats encompass a wide array of risks that can compromise the integrity, availability, and confidentiality of an organization’s data and systems. From ransomware attacks that lock down critical files to phishing campaigns that trick employees into revealing sensitive information, these threats are a constant challenge. Some common network security threats include: Strategies to Combat Network Security Threats The ever-evolving landscape of network security threats demands a comprehensive and proactive approach to protection. While no security strategy is foolproof, the implementation of multifaceted defenses significantly reduces the risk of successful attacks. By embracing a combination of advanced tools, employee education, strict access controls, and regular assessments, organizations can fortify their network security posture and stay ahead of emerging threats. In a world where cybercriminals are constantly innovating, the key to success lies in continuous vigilance, adaptability, and a commitment to safeguarding digital assets and sensitive information.
Network Security Management: Unveiling Common Challenges

Network security management has reached a new landmark at various levels, from the most basic home office up to a large enterprise. In the cyber attack world that is, unfortunately, more sophisticated and frequent, this is an area in which many businesses -from small startups to large enterprises- rely upon to secure their networks to protect sensitive data, digital assets, and, most importantly, customer information. An example of the repercussions that a breach in network security can cause is data loss, financial loss, damage to reputation, even regulatory penalties. Network security management is the practice of administering and securing the network infrastructure of an organization in order to avoid unauthorized access, misuse, and any form of breach in data. It includes the various technique and methods, tools, and best practices that establish a network’s requisite security components, which can include firewalls, intrusion detection systems (IDS), encryption, and access control measures. This all-inclusive guide addresses the highly critical aspect of network security management, its key ingredients, and the best practices for managing network security at the end of the lecture. In addition, we will also address how it is possible to enhance network security with appropriate tools and technologies while providing a proactive approach to the protection of ports from cyber threats. What is network security management? Network security management refers to the activities through which one manages monitors and protects the integrity of the network-from both internal and external cyber threats. These activities involve developing network security policies, implementing protective measures, continuing monitoring of traffic, conducting vulnerability assessments, and assuring compliance with security standards and regulations. The overall aim of network security management is to protect sensitive information, resources, and systems of the organization from cybercriminals and malevolent actors exploiting weaknesses in its network. It is achieved through the combined action of technology, processes, and people working together in risk management. Some functions of network security management are: Access control: Determining who can access the network and what she or he can do once connected to it.Data protection: safeguarding sensitive data against unauthorized access as well as retention and modification.Intrusion detection and prevention: detection and prevention of unauthorized or malign activity within the network.Security surveillance: about continuous surveillance of the network with respect to its development, vulnerability, indicator of suspicious activities, or potential threats.Application security risk management: identification of the possibility of a security breach in an application system and risk mitigation steps in the event of such an occurrence. The Importance of Network Security Management Network security management is essential for several reasons, especially as organizations become more digital and dependent on technology. Some of the key reasons why network security management is critical include: 1. Preventing Cyberattacks Cyberattacks are becoming increasingly frequent, sophisticated, and damaging. Network security management helps prevent attacks like hacking, phishing, malware, and denial-of-service (DoS) attacks by implementing strong defenses against these threats. Without proper network security management, a business is at risk of being targeted by cybercriminals who can exploit weak points in the network infrastructure. A breach can lead to loss of data, business downtime, and customer trust. 2. Protecting Sensitive Data Organizations store sensitive data such as personal information, intellectual property, financial records, and proprietary business data. Securing this data is vital to maintaining customer trust and adhering to privacy regulations. Network security management ensures that only authorized individuals can access sensitive data and that it is encrypted during transmission to prevent unauthorized access or theft. 3. Ensuring Compliance with Regulations Many industries are governed by stringent data protection regulations such as GDPR (General Data Protection Regulation), HIPAA (Health Insurance Portability and Accountability Act), and PCI DSS (Payment Card Industry Data Security Standard). Network security management ensures that an organization’s network and systems comply with these regulations by implementing the necessary security measures and controls. Failing to comply can lead to fines, legal consequences, and damage to the organization’s reputation. 4. Maintaining Business Continuity A strong network security management strategy helps reduce the risk of network downtime due to cyberattacks or security breaches. By proactively identifying and mitigating vulnerabilities, businesses can avoid disruptions caused by security incidents, ensuring that operations continue smoothly. 5. Safeguarding Brand Reputation A security breach can significantly damage an organization’s reputation. Customers and partners may lose trust if their personal data is compromised, leading to a loss of business. Effective network security management demonstrates an organization’s commitment to protecting its stakeholders, reinforcing customer loyalty, and enhancing its reputation in the marketplace. Key Components of Security Management To manage network security effectively, organizations must implement a multi-layered approach that involves various security components. Here are the key components of security management: 1. Firewall Management A firewall is one of the most critical components of network security. It acts as a barrier between a trusted internal network and untrusted external networks (such as the internet). Firewalls monitor incoming and outgoing traffic and block malicious traffic based on pre-established security rules. Effective security management involves configuring and maintaining firewalls to ensure they are properly set up to block unauthorized access while allowing legitimate traffic. Regular updates to firewall rules are essential to keep up with changing threats and attack methods. 2. Intrusion Detection and Prevention Systems (IDS/IPS) Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS) are used to detect and prevent unauthorized access or suspicious activity within a network. IDS identifies potential threats by monitoring network traffic for signs of malicious behavior, while IPS takes it a step further by actively blocking or mitigating the threats once they are detected. Integrating IDS and IPS into network security management helps identify and respond to security incidents in real-time, preventing data breaches and minimizing the impact of attacks. 3. Encryption Encryption is the process of converting data into a secure format that is unreadable to unauthorized users. When data is transmitted over a network, encryption ensures that even if intercepted, the data remains protected. Network security management includes implementing encryption protocols such as SSL/TLS for secure communication, VPNs (Virtual Private Networks)
Firewall Policy Optimization: A Guide to Firewall Management

In today’s digital landscape, where cyber threats are pervasive and evolving, an organization’s information security strategy is only as strong as its weakest link. Firewalls stand as essential sentinels, guarding the digital gates against unauthorized access and malicious intrusions. However, a firewall is only as effective as its policies. Enter firewall policy optimization – a crucial process that fine-tunes and refines these policies to ensure robust protection and streamlined network performance. In this comprehensive blog post, we delve into the importance of firewall policy optimization, its key considerations, best practices, and how it contributes to a fortified cybersecurity posture. The Significance of Firewall Policy Optimization Firewalls play a pivotal role in protecting an organization’s digital assets by regulating network traffic, preventing unauthorized access, and mitigating cyber risks. Yet, over time, the accumulation of rules and policies can lead to policy sprawl – a situation where policies become overly complex, redundant, and difficult to manage. This can inadvertently create security gaps or impact network performance. Firewall policy optimization emerges as the remedy, focusing on refining these policies to align with the organization’s security objectives, compliance requirements, and operational needs. Key Considerations for Firewall Policy Optimization Best Practices for Effective Optimization Impact of Firewall Optimization on Cybersecurity In an era of persistent cyber threats, firewall policy optimization emerges as a linchpin of effective cybersecurity strategy. By refining and fine-tuning firewall policies, organizations can achieve a delicate equilibrium between stringent security measures and operational agility. The process ensures that the organization’s digital fortress remains robust, adaptable, and resilient against an ever-evolving threat landscape. Through regular reviews, meticulous collaboration, and adherence to best practices, firewall policy optimization becomes a cornerstone of a proactive cybersecurity approach, safeguarding critical assets and bolstering trust among stakeholders in an increasingly digital world.
Understanding Cyber Network Security: Importance and Impact

In today’s interconnected digital landscape, the term “cyber network security” has become increasingly crucial. As organizations and individuals rely heavily on technology for communication, transactions, and information exchange, the need to safeguard networks from malicious threats has never been more paramount. In this blog post, we will delve into the fundamentals of network security, its significance, and the reasons why it holds a pivotal role in our digital lives. Defining Cyber Network Security Cyber network security encompasses a range of practices, technologies, and protocols designed to protect computer networks, systems, and data from unauthorized access, breaches, and cyberattacks. It is a multidimensional approach that involves various strategies to ensure the confidentiality, integrity, and availability of digital assets. These strategies include but are not limited to firewalls, encryption, access controls, intrusion detection systems, and regular software updates. The Importance of Cyber Network Security In conclusion, cyber network security is not a mere option but a necessity in our technology-driven world. It serves as a shield against a barrage of cyber threats that can compromise sensitive data, disrupt operations, and cause irreparable damage to an individual or organization. By investing in robust network security measures, we can ensure the confidentiality, integrity, and availability of data, thereby safeguarding our digital future. As technology continues to evolve, so do cyber threats, making the role of network security even more critical in the years to come.
Emerging Trends in Network Firewall Security: Ensuring Robust Protection in a Rapidly Evolving Digital Landscape

Cyber threats are becoming increasingly sophisticated, network firewall security plays a pivotal role in safeguarding organizations’ critical assets. As technology advances, so do the tactics employed by malicious actors, necessitating the adoption of emerging trends in network firewall security. In this blog post, we will explore the latest developments in this field, highlighting key strategies and techniques to ensure robust protection. Whether you’re an IT professional, business owner, or simply interested in the evolving landscape of cybersecurity, this article will provide valuable insights into the future of network firewall security. Machine Learning-Powered Firewalls: One of the most promising trends in network firewall security is the integration of machine learning algorithms. Machine learning-powered firewalls can analyze vast amounts of network data in real-time, identifying anomalies and potential threats with exceptional accuracy. By continuously learning from new data patterns, these intelligent firewalls can adapt and evolve, effectively mitigating emerging risks. Cloud-Based Firewall Solutions: With the widespread adoption of cloud services, traditional on-premises firewalls face limitations in protecting cloud-hosted applications and data. Cloud-based firewall solutions are emerging as a viable option, offering scalable, flexible, and centrally managed security for distributed environments. These solutions provide seamless integration with cloud platforms, enabling organizations to maintain consistent protection across their entire infrastructure. Next-Generation Firewall Capabilities: Next-generation firewalls (NGFWs) are evolving to encompass advanced features beyond traditional packet filtering. These advanced capabilities include intrusion prevention systems (IPS), deep packet inspection (DPI), application-level controls, and integrated threat intelligence. NGFWs enable granular control over network traffic, enhancing security posture and enabling organizations to implement sophisticated access policies. Zero Trust Network Architecture: As network perimeters dissolve with the rise of remote work and cloud adoption, the concept of Zero Trust Network Architecture gains prominence. This approach assumes no inherent trust for any user or device, enforcing strict access controls and continuous authentication. By implementing Zero Trust principles, organizations can significantly minimize the impact of security breaches and prevent lateral movement within the network. Software-Defined Networking (SDN) Integration: The convergence of network firewall security and software-defined networking (SDN) presents new opportunities for enhanced protection. SDN integration allows for dynamic traffic routing and real-time policy enforcement, improving threat response times and reducing attack surface areas. By leveraging SDN capabilities, organizations can achieve greater visibility and control over their network traffic, enhancing overall security. Threat Intelligence and Information Sharing: Network firewall security is no longer limited to individual deployments but extends to a collaborative approach. Threat intelligence platforms and information sharing initiatives enable organizations to leverage collective knowledge and stay ahead of emerging threats. By participating in threat intelligence communities, organizations can proactively identify new attack vectors, adapt their firewall configurations, and fortify their defenses. Mobile Device and IoT Firewall Security: As mobile devices and Internet of Things (IoT) devices proliferate, network firewall security must extend its protection beyond traditional endpoints. Mobile device management (MDM) solutions and dedicated firewall measures for IoT devices are gaining traction. By implementing firewalls that cater specifically to these endpoints, organizations can mitigate the risks associated with mobile and IoT-related cyber threats. As the cybersecurity landscape evolves, network firewall security must adapt to address new and emerging threats. By embracing the emerging trends we’ve discussed, organizations can bolster their defenses and safeguard critical assets. Machine learning-powered firewalls, cloud-based solutions, next-generation firewall capabilities, Zero Trust Network Architecture, SDN integration, threat intelligence sharing, and dedicated mobile/IoT firewall security are key areas to focus on. By staying informed about these developments, organizations can.
Types Of Filtering Concepts in Firewall Security

A firewall is a network security device or software that acts as a barrier between an internal network and external networks, such as the internet. It monitors and controls incoming and outgoing network traffic based on predetermined security rules. The primary purpose of a firewall security is to protect a network or computer system from unauthorized access and potential threats, such as malware, hackers, or malicious activities. Firewalls can be implemented in various forms, including hardware devices, software applications, or a combination of both. They analyze network traffic packets, inspecting the source and destination addresses, ports, protocols, and other attributes to determine whether to allow or block the traffic based on the configured rules. Firewalls can be configured to filter and block specific types of network traffic, such as certain ports or protocols, and can also provide additional security features such as intrusion detection and prevention, virtual private network (VPN) support, and logging capabilities to track and analyze network activity. By enforcing security policies and controlling network traffic, firewalls help to reduce the risk of unauthorized access, data breaches, and other cyber threats, thereby enhancing the overall security of a network or computer system. Packet filtering is a fundamental concept in firewall security. It involves examining individual network packets as they pass through a firewall and making access control decisions based on predetermined rules or policies. Here’s how packet filtering works: Packet Inspection: When a network packet arrives at the firewall, the firewall inspects the header information of the packet. This includes details such as source and destination IP addresses, port numbers, and protocol types (such as TCP or UDP). Rule Evaluation: The firewall compares the packet’s header information against a set of predefined rules or policies. These rules specify what types of traffic are allowed or blocked based on specific criteria. Access Control Decision: Based on the evaluation of the rules, the firewall makes an access control decision for the packet. The decision can be one of the following: Allow: If the packet matches an allowed rule, the firewall permits the packet to pass through and reach its destination. Block: If the packet matches a blocked rule, the firewall drops or rejects the packet, preventing it from reaching its intended destination. Default Behavior: If a packet does not match any of the defined rules, the firewall applies a default behavior. This can be either allowing or blocking the packet, depending on the firewall’s configuration. Commonly, firewalls are set to block packets that do not have a matching rule. Packet filtering can be based on various criteria, such as source and destination IP addresses, port numbers, and protocol types. For example, a firewall might have rules that allow incoming web traffic (HTTP) on port 80, but block incoming email traffic (SMTP) on port 25. Packet filtering is an effective mechanism for enforcing access control and filtering network traffic at the network layer (Layer 3) of the TCP/IP protocol stack. It helps protect against unauthorized access attempts, malicious traffic, and certain types of network-based attacks. However, it is important to properly configure and maintain packet filtering rules to avoid unintended security gaps or false positives/negatives. Apart from packet filtering, firewalls employ additional filtering mechanisms to enhance network security. Some of these mechanisms include: Proxy Filtering: Firewalls can act as proxies for specific protocols, such as HTTP or FTP. Instead of directly forwarding packets, the firewall establishes a connection with the remote server on behalf of the client. This allows the firewall to inspect and filter the content of the communication at the application layer. URL Filtering: Firewalls can implement URL filtering to control access to specific websites or categories of websites based on their URLs or domain names. This firewall security filtering mechanism helps enforce acceptable use policies, restrict access to malicious or inappropriate content, and prevent employees from visiting unauthorized websites. Content Filtering: Content filtering allows firewalls to inspect and analyze the actual content of network traffic, including web pages, email attachments, or file transfers. By using content filtering, firewalls can block or allow traffic based on predefined rules related to keywords, file types, or content categories. Malware Filtering: Firewalls can incorporate malware filtering capabilities to identify and block network traffic associated with known malware, viruses, or other malicious activities. This filtering mechanism helps protect against malware downloads or communication with malicious command-and-control servers. Deep Packet Inspection (DPI): Deep packet inspection goes beyond traditional packet filtering by examining the payload or contents of network packets at a granular level. It allows firewalls to inspect and analyze the complete packet, including the application-layer data, to detect specific patterns or behaviors associated with attacks or policy violations. Application Control: Firewalls can implement application control policies to regulate the use of specific applications or protocols. This mechanism allows organizations to enforce restrictions on applications that may pose security risks, consume excessive bandwidth, or violate compliance policies. Behavior-based Filtering: Some advanced firewalls incorporate behavior-based filtering, also known as anomaly detection. By monitoring network traffic and comparing it to normal patterns, these firewalls can identify and block suspicious or abnormal behavior that may indicate a potential attack or security breach. These additional filtering mechanisms provide firewall security with more granular control and visibility into network traffic, enabling them to enforce security policies at different layers of the network stack and mitigate various types of threats.


